The failure occurred on February 15 after the activation of the Moonwell DAO proposal MIP-X43, which enabled contracts using Chainlink OEV on the Base and Optimism networks.
Technical flaw
One of the oracles was configured incorrectly and mispriced Coinbase Wrapped ETH (cbETH) in U.S. dollars. Instead of multiplying the cbETH/ETH rate by the ETH/USD price, the system only transmitted the token-to-token ratio. As a result, the oracle displayed cbETH at around $1.12 instead of approximately $2,200.
Impact on users
The abnormally low price triggered a wave of liquidations. Trading bots targeted positions collateralized with cbETH, repaying roughly $1 of debt and receiving 1,096.317 cbETH in return.
This wiped out most or all cbETH collateral for many borrowers, leaving them with significant residual debt. At the same time, some users were able to post minimal collateral to borrow cbETH at the distorted price.
“As soon as the issue was identified, our risk manager @anthiasxyz promptly reduced the cbETH borrow cap to 0.01 to limit further risk to the protocol,” Moonwell representatives said.
Is vibe coding to blame?
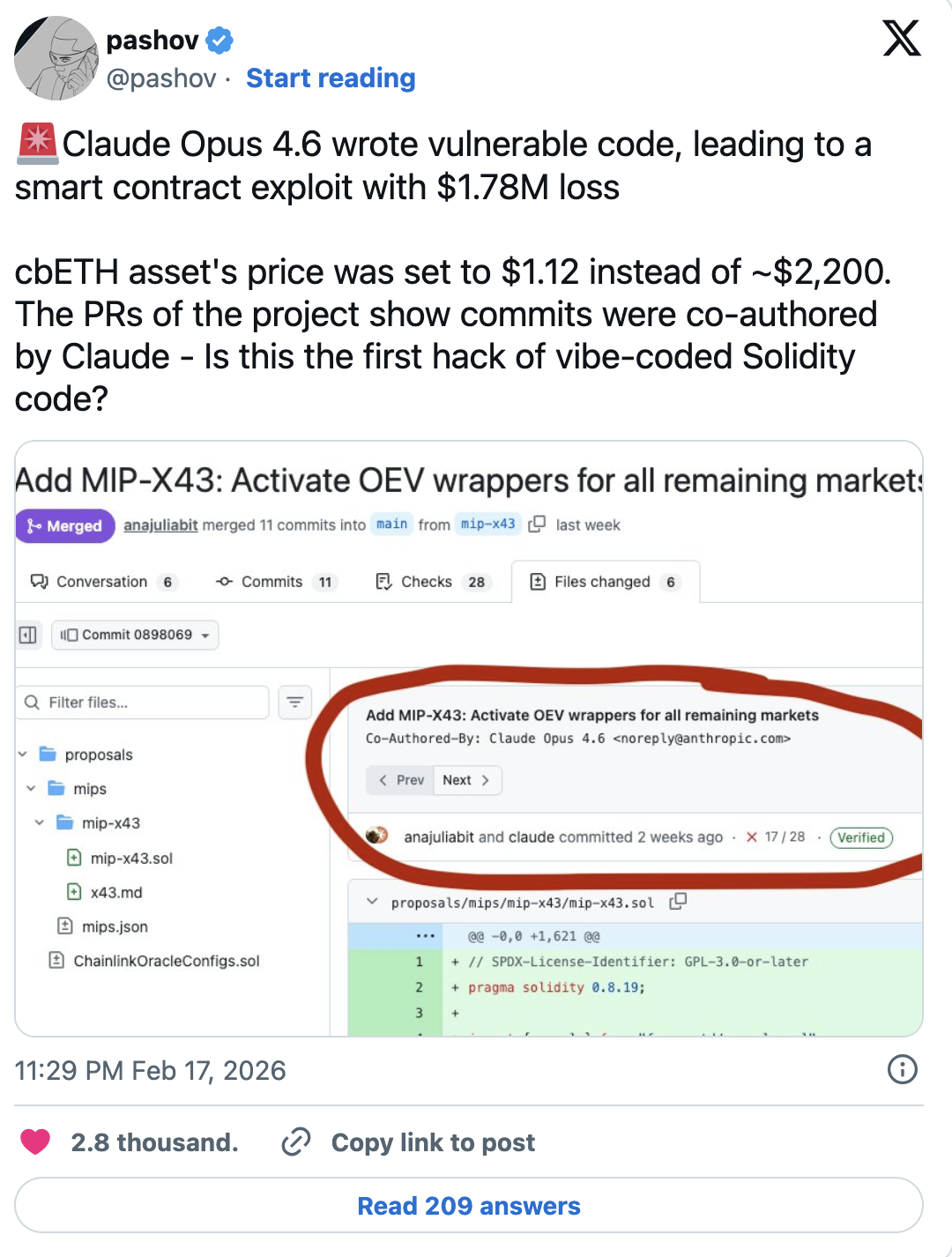
Smart contract auditor Pashov noted that commits related to Moonwell were co-authored with Claude Opus 4.6.
“Claude Opus 4.6 wrote vulnerable code, which led to a smart contract exploit with losses of $1.78 million. […] Is this the first Solidity exploit caused by vibe-coded code?” he wrote.
He added that an AI is ultimately supervised by a human who reviews the output—and potentially by a security auditor—so blaming the neural network alone would be incorrect. Still, the incident “raises questions” about the risks of vibe coding.
This programming approach is becoming increasingly widespread, despite growing criticism from experienced developers and security specialists.
The Moonwell incident highlights how a single oracle misconfiguration can cascade into large-scale losses in DeFi. While AI-assisted “vibe coding” may accelerate development, it does not replace rigorous human review and security auditing. The case underscores the need for stricter controls when deploying AI-generated code in financial protocols.


 ES
ES  EN
EN